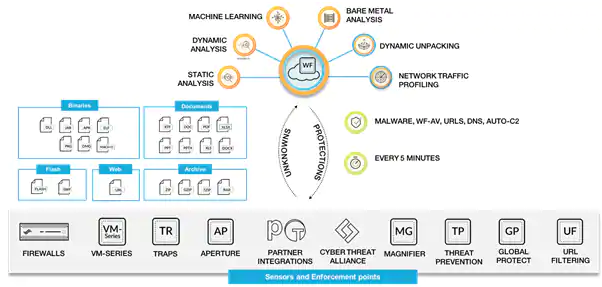
Palo Alto WildFire® provides detection and prevention of zero-day malware using a combination of malware sandboxing and signature-based detection and blocking of malware. WildFire extends the capabilities of Palo Alto Networks next-generation firewalls to identify and block targeted and unknown malware.
With WildFire you get immediate automated protections across the platform, stopping malware, malicious URLs, DNS and C2.
Find the Unknown With a Unique Multi-Technique Approach
WildFire goes beyond traditional approaches used to detect unknown threats,
bringing together the benefits of four independent techniques for high-fidelity and
evasion-resistant discovery, including:
- Dynamic analysis – observes files as they detonate in a purpose-built,
evasion-resistant virtual environment, enabling detection of zero-day exploits
and malware using hundreds of behavioral characteristics. - Static analysis – complements dynamic analysis with effective detection of
malware and exploits, as well as providing instant identification of malware
variants. Static analysis further leverages dynamic unpacking to analyze threats
attempting to evade detection using packer tools. - Machine learning – extracts thousands of unique features from each file, training
a predictive machine learning model to identify new malware, which is not possible
with static or dynamic analysis alone. - Bare metal analysis – detonates evasive threats in a real hardware environment,
entirely removing an adversary’s ability to deploy anti-VM analysis techniques.
Automated Orchestration of Prevention
When zero-day exploits or malware are discovered by any WildFire subscriber, the service automatically orchestrates enforcement of high-fidelity, evasion-resistant protections for all WildFire subscribers in as few as five minutes from first discovery anywhere in the world.
WildFire also forms the central prevention orchestration point for the Security Operating Platform, allowing the enforcement of new controls through:
- Threat Prevention to block malware, exploits, and command-and-control activity.
- URL Filtering with PAN-DB for the prevention of newly discovered malicious URLs.
- AutoFocus™ contextual threat intelligence service, enabling the extraction, correlation and analysis of threat intelligence
with high relevance and context. - Traps™ advanced endpoint protection and Aperture™ SaaS security service for real-time verdict determination and threat
prevention. - Integration with our technology partners for verdict determination on third-party services with the WildFire API.
Most Advanced Malware Analysis Environment
The WildFire engine is based on two primary components:
- Custom-built hypervisor: Built from the ground up to avoid use of commonly used, open source emulation software that has become trivial to evade, the WildFire hypervisor is immune to commoditized anti-VM analysis techniques used to evade detection in traditional malware analysis environments. The custom hypervisor also provides a flexible framework to continue building advanced detection and evasion-resistant capability into WildFire in the future.
- Bare metal analysis: The most sophisticated threats can potentially observe that they are being examined in an advanced virtual environment and fail to fully detonate. To address this class of advanced attacks, WildFire has the ability to automatically analyze advanced threats in real hardware systems using our bare metal analysis engine. Now, even the most evasive threats can be conclusively identified and prevented. Within the malware analysis environment, WildFire executes suspicious content in the Windows® XP, Windows 7, Windows 10, Android® and macOS® operating systems, with full visibility into commonly exploited file formats, such as EXE, DLL, ZIP, 7ZIP, RAR Archive, Mach-O, Mach-OSX DMG, ELF (Linux) and PDF, as well as Microsoft Office documents, Java files.
WildFire identifies files with potential malicious behaviors and delivers verdicts based on their actions, through:
- Complete malicious behavior visibility – identifies threats in all traffic across hundreds of applications, including web
traffic, email protocols like SMTP, IMAP and POP, as well as file sharing protocols like SMB and FTP, regardless of ports
or encryption. - Changes made to host – observes all processes for modifications to the host, including evidence of exploitation, persistence
mechanisms, data encryption or system destruction techniques. - Suspicious network traffic – performs analysis of all network activity produced by the suspicious file, including backdoor
creation, downloading of next-stage malware, visiting low-reputation domains, network reconnaissance and much more. - Anti-analysis detection – monitors techniques used by advanced malware that are designed to avoid VM-based analysis,
such as debugger detection, hypervisor detection, code injection into trusted processes, disabling of host-based security
features and much more. - Threat intelligence, analytics and correlation
WildFire Requirements
WildFire analysis of certain file types requires the following version, or a newer version, of PAN-OS:
- Baseline WildFire functionality requires PAN-OS 4.1+
- DF, Java, Office and APK analysis requires PAN-OS 6.0+
- Adobe Flash and webpage analysis requires PAN-OS 6.1+