Author's details
Date registered: 25th July 2015
Latest posts
- Information Security RISK response strategies — 2nd February 2021
- Time to crack passwords — 2nd March 2020
- Connection throttling iRule — 23rd February 2020
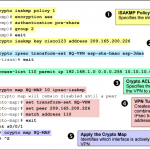
- IPSec VPN on Cisco ASA — 6th April 2019
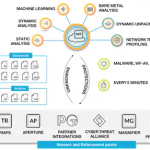
- Palo Alto WildFire explained — 6th April 2019