A POODLE attack is an exploit that takes advantage of the way some browsers deal with encryption. POODLE (Padding Oracle On Downgraded Legacy Encryption) is the name of the vulnerability that enables the exploit.
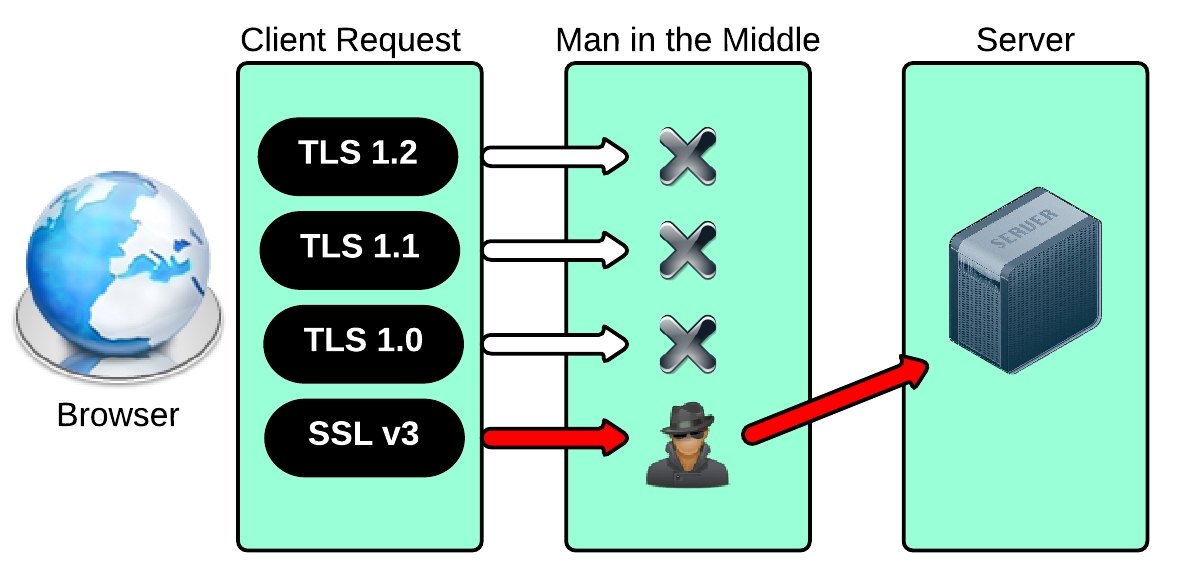
POODLE can be used to target browser-based communication that relies on the Secure Sockets Layer (SSL) 3.0 protocol for encryption and authentication. The Transport Layer Security (TLS) protocol has largely replaced SSL for secure communication on the Internet, but many browsers will revert to SSL 3.0 when a TLS connection is unavailable. An attacker who wants to exploit POODLE takes advantage of this by inserting himself into the communication session and forcing the browser to use SSL 3.0.
The attacker is then free to a exploit design flaw in SSL 3.0 that allows the padding data at the end of a block cipher to be changed so that the encryption cipher become less secure each time it is passed. To prevent a POODLE attack that forces a browser to degrade to SSL 3.0, administrators should check to see that their server software supports the latest version of TLS and is configured properly.
Google researchers Bodo Moller, Thai Duong and Krzysztof Kotowicz discovered (and named) the POODLE vulnerability and warned the IT community that the only way to prevent POODLE attacks is to stop using SSL 3.0. Mozilla and Microsoft have responded by creating ways for end users to disable SSL 3.0 manually in Firefox and Internet Explorer (IE).
Apple, Google, Mozilla and Microsoft have all announced plans to stop supporting SSL 3.0 in the near future.
Aug 25

